Link to the appellate opinion in .pdf on courthouse news.com
Link to the appellate opinion in .pdf on courthouse news.com
Another summary on jdsupra.com
Some screenshots of the opinion follow my notes
Federal circuit:- affirms PTAB’s rejection of 20 claims against Proxyconn
– reminds court that it cannot be unreasonable in analyzing claim construction for its broadest reasonable interpretation (BRI… Means the patent trials and appeals board has wide latitude to see claims as broadly as can be reasonably construed, increasing the odds that a claim is claiming too broadly, overstepping prior art and teachings to be a valid patent).
– affirms denial of motion to amend
– specifically doesn’t touch the requirement that appellants to PTAB demonstrate patentability over ALL prior art known to the appellant
– encourages PTAB to consult the application’s prosecution history (interesting because it was believed that PTAB doesn’t have-to, in order to conjure what it believes to be the BRI

Sidenote: I always feel like the subject matter is the way to remember what happened. All lawyers should strive to be focused upon the precedent in wielding a new legal precedent, but I often wonder whether patent law should be substantively more focused upon the subject matter, if only by relative comparison against other parts of the law. Software and IT are especially rife with activity because they so rapidly generate increments of purportedly-new embodiments that both administration and judicial mechanisms cannot possibly keep up. at any rate, here’s a taster of the subject matter.
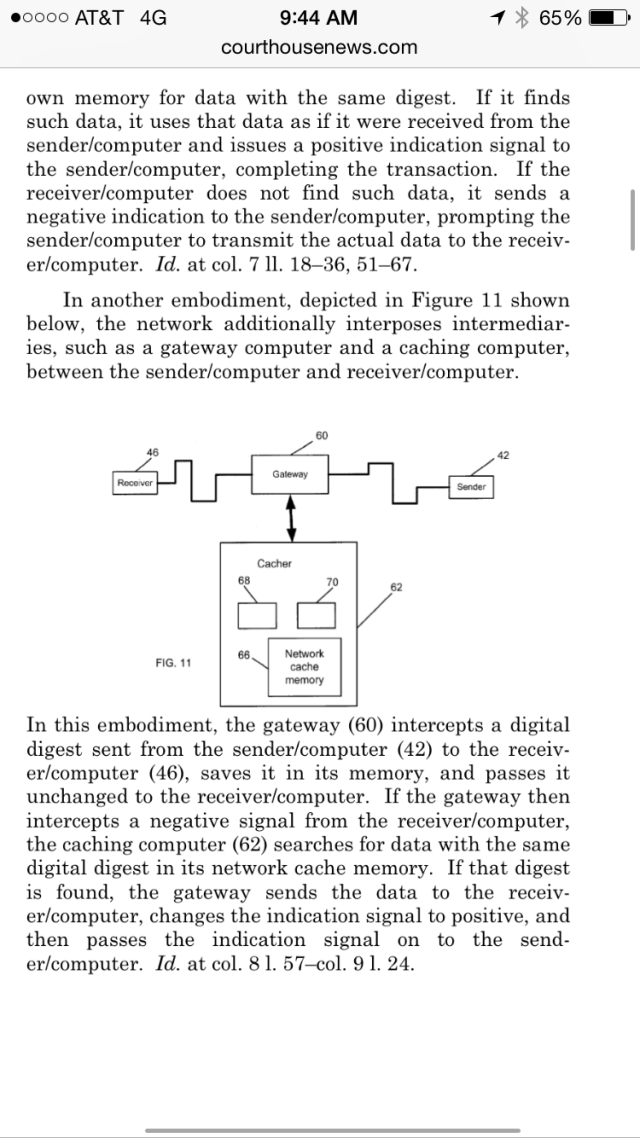
Look how specific that is! A “receiver” computer requests data, the “sender” computer checks to see if it has the data and then sends a “digest,” a sort of indicator of a piece of data back to the sender computer to say “yes I have it, but don’t you already have that?” The receiver computer then checks its own memory to see if the digest points to that data which it just attempted to retrieve. So basically, this is designed to alleviate the sender computer from having to send data to the receiver computer if the receiver computer has that data already stored in its memory. So that is a conversation between two computers. Then, the more sophisticated embodiment puts a gateway between the two. This keeps a copy of the digest during the sending and the data from a previous transmission through the network. On the way out from the sender, it keeps a copy of the digest. If the receiver computer returns back to the sender computer after searching its own memory with the digest, that it does not have the data, then the gateway searches its own memory using the digest, and then returns that data to the receiver, and then changes the negative report to a positive one to send back to the sender computer.
This seems all designed to prevent the sender from having to do so much. Presumably, requests are being made all the time for the same data. When something receives the data, it keeps that data in its own memory for at least a little while. While it’s out there, if it can be routed around without having to get it from the server again, then the sender can just worry about sending out data only when it was first asked. That’s presuming that the Gateway computer is working overtime to essentially store data as something other than the sender.
Now, I can’t possibly know from this how this is currently being practiced. Maybe “data” is so specific that only one user will be making the identical sort of request, such that this data is particularized, and is something other than just a computer storing data that was sent from the server. If I had to take a wild guess at what the above might cover, I wouldn’t be surprised if proxyconn wouldn’t be ashamed to assert it against a method in which a website that’s serving the results every time I request that cargurus.com tell me about any 2008 to 2010 BMW 535i sport in Raleigh. But look what is happening with the claim construction.
“Two other computers” is how Proxyxonn attempted to claim the communications between receiver and sender! That’s ridiculous. I like BRI here. If you go that broad, you shouldn’t get the benefit of specifying much more narrowly in your specification. It’s a fair argument that this is chastising overbroad construction, rather than whether or not a claim really is tailored to the degree to which an infringer has overstepped what was disclosed, rather than whether or not a claim is unsupported to the degree that the grantee has genuinely supported their claim. There is the risk that the board would invalidate the claim in its entirety, and therefore it’s a warning to applicants that they risk the protection of an entire claim if they don’t toe the line of making claim language directly fit what they are disclosing. It’s a reason for applicants to voluntarily cut-back the scope that they won, if it is in excess of what they really are willing to concede that they have not invented.